Top Cybersecurity Trends to Watch For in 2020
With one specific infection hoarding the spotlight right now, cybersecurity concerns appear to arrive in a removed second. Sadly, cybercriminals don’t appear to be taking a day off. In this post, we’ll go over the top cybersecurity patterns guarding the web in 2020.

SEE ALSO: The Cybersecurity Review
Top 4 Cyberattack Trends
The development of robust security technologies has spurred cyberattackers to up their game, going as far as to adopt artificial intelligence (AI) and machine learning (ML) to break through the latest cybersecurity measures. Hence, it has become imperative to keep updating the cyber defense technologies to maintain an edge in this era of cyber warfare. Of all the cyber threats, there are a few that stand above the others in terms of damage and vulnerability.
Dwindling Visibility in Corporate IT
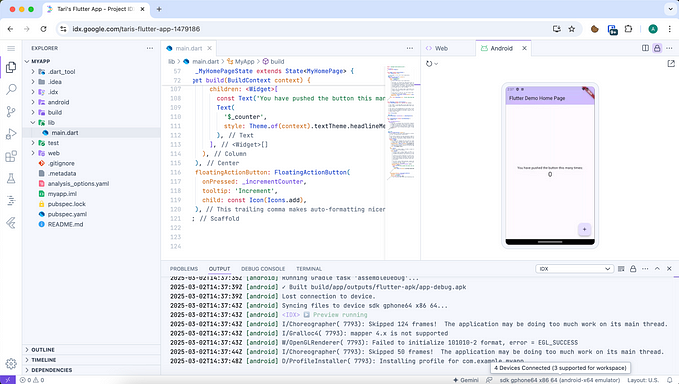
The digital transformation across the industrial sector has urged organizations into adopting hybrid cloud infrastructures to drive flexibility as well as ease of access. However, migrating assets and operations into the cloud can result in organizations losing control and visibility over their processes as the vendors manage the cloud platform. Enterprises often struggle to secure their applications and eliminate vulnerabilities over the cloud. It is essential for organizations to create comprehensive, up to date inventory of assets, including hardware, software, and user data.
SEE ALSO: The Cybersecurity Review
Vulnerability in the Cryptocurrency Sector

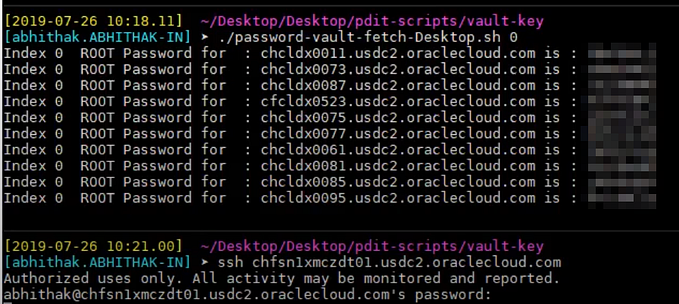
The lack of investment by law enforcement agencies in the cryptocurrency sector is attracting cybercriminals from all over the world. The cryptocurrency organizations are focused on staying afloat in the volatile landscape, paying little attention toward cybersecurity. It has incentivized attackers to develop sophisticated systems designed to conduct large-scale theft and digital coin scams. Hence, it is necessary for crypto asset owners to remain vigilant and secure their devices with up to date security solutions from reputed vendors.
Cybercriminals Leveraging AI and ML
Cybercriminals today are flexible enough to keep up with the innovations in technology, leveraging AI and ML for automating sophisticated attacks. Unlike many cybersecurity organizations who employ modern techniques for the sake of marketing, cybercriminals utilize AI and ML to augment their cyberattacks. Hence, organizations need to incorporate AI and ML in their cyber defense strategies to counter advanced threats.

SEE ALSO: The Cybersecurity Review
Impact of GDPR
In the wake of compliance requirements, organizations are ignoring the functional security requirements of their infrastructure. Most organizations focus most of their resources in avoiding GDPR sanctions by employing formalistic strategies rather than implementing practical approaches to deal with cybersecurity and privacy. Compliance is necessary, but so is the incorporation of robust security strategies.
Top 3 Cybersecurity Trends that Modern Businesses Should Look out For:

Cybersecurity is all set to impact the enterprises, security professionals and businesses of all sizes in future. The corporate world is most like affected by high-profile data breaches and ransomware attack. The cyber threat is growing in every sized business, which leads to loss of revenue, data breaches and sometimes company downfall as well. Biometric hacking and an increase in phishing attacks are among the top cybersecurity threats. Attackers stop at nothing to hijack identities and evade detection through latest techniques. These security trends will help in mitigating cyber risks to a great extent.
SEE ALSO: The Cybersecurity Review
• Operationalizing GDPR
The General Data Protection Regulation (GDPR) needs every business to protect the privacy and personal data of the citizens. The penalties for non-compliance are high, and the GDPR takes a broad view of what constitutes personal data, making this a potentially tough duty. A proactive approach to data privacy is beneficial for businesses trading in developed countries.
• Managing managed and Unmanaged Devices

The number and range of mobile devices employed by users continue to grow; enterprise networks have had an uphill struggle to mitigate the risks involved. The Internet of Things (IoT) has linked many connected devices, many of which have little or no built-in security, to previously secure networks resulting in an exponential rise in exploitable endpoints.
SEE ALSO: The Cybersecurity Review
• Phishing Scams to Soar

Email attacks are growing day by day, leaving organizations scrambling for new ways to reduce risk and better detect and remediate threats. These phishing attacks can be curbed by monitoring email traffic more closely. All systems should be laced with the latest security patches and updates. Files received into the company’s server should be tracked to identify where it originates from and ends up.
In future, there will be a paradigm shift in ways companies will use and manage data. Companies should re-assess their security posture and ensure adequate measures and controls are implemented to safeguard against today’s cyber-attacks.
See Also: